Understanding Cryptocurrency Bounty Programs: Risks & Rewards
While these bounty programs are mostly used to reward developers for spotting vulnerabilities in code, they’ve expanded to not only offer general coding requests, but also marketing-like services, such as writing content and tweeting out links.
But bounty hunters also play an important, active role in helping bring criminals to justice who seek to disrupt the benefits digital currency brings.
How It Works
Source: HackerNoon
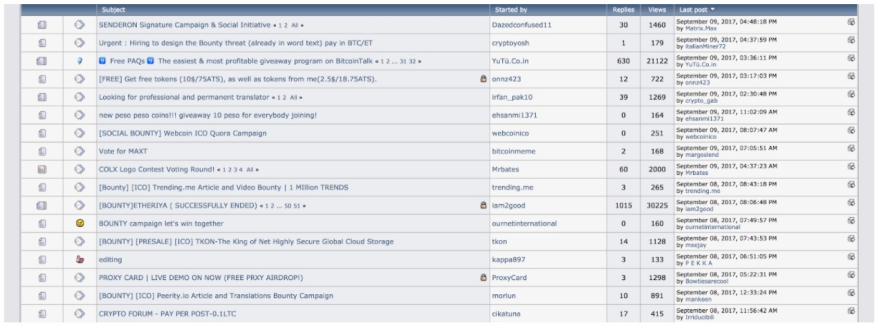
Whether you are tech-savvy or non-technical, bounty hunting provides numerous tasks that can be completed. All new cryptocurrency projects need marketing to help sell their coins during its ICO. Many of these projects choose to do their own marketing in-house or using a marketing agency. But they also add a “bounty program.
A bounty program offers cryptocurrency in exchange for promotion, if the ICO turns out to be a success. In other words, payment is never guaranteed up and until the ICO closes. Each given cryptocurrency has its own percentage of their tokens reserved to be given for these bounty programs.
The program is broken down into two stages:
The first stage, pre-ICO, is marketed to prospective investors, including social media influencers, blog writers, and BitcoinTalk Signature bounty hunters.
The second stage, known as the post-ICO stage, which focus on the final touchups to the released blockchain. During this stage, bounty rewards are offered to translators, who help distribute it globally, by putting together translated documents on the development and marketing.
Fund information
- Cryptocurrency Airdrops: A Comprehensive Guide for Beginners
- Cryptocurrency Tokens Explained: Types, Functionality & Tokenization
- Libra Cryptocurrency: A Comprehensive Overview
- Understanding Cryptocurrency: A Beginner's Guide to Digital Currency
- Cryptocurrency Explained: A Beginner's Guide to Digital Currency
- Initial Coin Offerings (ICOs): A Comprehensive Guide
- Understanding Cryptocurrency: A Comprehensive Beginner's Guide
- Cryptocurrency Mining Explained: How New Coins Are Created
- Ethereum Explained: A Comprehensive Guide to the Blockchain Platform
-
 MAGACOIN: Understanding the Trump-Themed Cryptocurrency
MAGACOIN: Understanding the Trump-Themed CryptocurrencyWelcome a new cryptocurrency to the market, MAGACOIN.How would you feel when I say there is a new crypto coin, which is a Donald Trump-themed cryptocurrency? Funny, isn’t it? Well, then let’s welcome ...
-
 Understanding Cryptocurrency: A Comprehensive Guide to Common Questions
Understanding Cryptocurrency: A Comprehensive Guide to Common QuestionsCryptocurrencies like Bitcoin, Ethereum, and dozens of lesser-known digital currencies frequently appear in the news, often following wild price spikes, and sometimes to cover the revolutionary blockc...


